Posted originally on Nov 24, 2025 by Martin Armstrong |
The House Oversight Committee ordered Bill and Hillary Clinton to appear in court for depositions in December regarding their relationship with Jeffrey Epstein and Ghislaine Maxwell. The Clintons have always represented the peak of the political establishment, and with that comes a long trail of scandals. Will the Clintons finally have their day in court?
“Given the admission that your clients possess some relevant information, your position amounts to a demand that the Committee forgo in-person testimony, potentially relevant to its legislative oversight,” the powerful GOP chairman said.
David Kendall, acting attorney for the Clintons, claims the Clintons fully condemn Epstein’s actions and understand the public’s need for transparency. “Former President Clinton and former Secretary Clinton welcome legitimate oversight in this matter that is grounded in fact,” Kendall added, followed by downplaying his clients’ relationship to Maxwell and Epstein.
The committee insisted that the Clintons appear in court. “Additionally, your suggestion that your clients’ testimony would not be relevant to the stated purposes of the Committee’s investigation because the events in question took place outside of the Clintons’ respective official duties misses the Committee’s point,” Comer added. “It is precisely the fact that President Clinton and Secretary Clinton each maintained relationships with Mr. Epstein and Ms. Maxwell in their personal capacities as private citizens that is of interest to the Committee.”
Interestingly, the court of public opinion has always been far more interested in personal matters than actual crimes against humanity. Clinton affiliates have a high suicide rate. Bill’s administration was littered with issues from his mishandling of Al-Qaeda to Whitewater and the banking scandal. Haiti, Russia, accepting bribes from Chinese nationals—the list of corruption on a global scale was endless during Bill’s leadership and continued as Hillary took over. Yet, the blood on their hands is less remembered than a stain on a dress. The court of public opinion was most concerned about his affair with Monica Lewinsky.
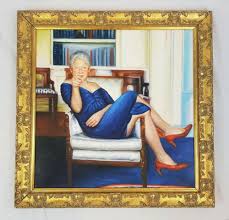
The sexual debauchery that took place on Epstein’s island caused a public uproar; the people will not let the government dismiss this case. As for their connection to Epstein, the Clintons used his intricate ties to create RussiaGate and infiltrate not only public perception of Trump but also foreign governments’ perception of Trump. The public is not interested in these matters per se, but they do want to know why the Clintons were personally associated with Epstein and Maxwell. That picture of Bill Clinton hanging on Epstein Island has been viewed worldwide.
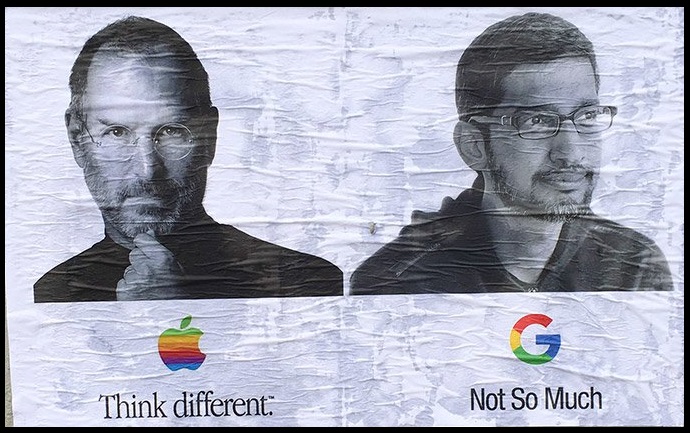
Al Capone was arrested for tax evasion. Former Nazi war criminals were arrested in the US for evading immigration officials. And now, the Clintons are being called to answer for lesser crimes that could bring their extensive legacy of destruction to light. The significance of the Clintons being called to testify is not about whether they did or did not engage in wrongdoing at Epstein’s properties. The real significance is that the system is no longer capable of protecting its former kings and queens.