Posted originally on the conservative tree house on August 27, 2022 | Sundance
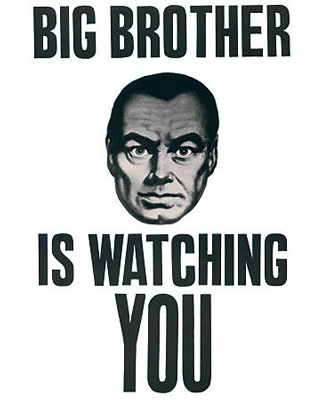
The suspicions surrounding Jack’s Magic Coffee shop are not new. {Go Deep} Indeed, the recent whistleblower claims of data insecurity seem to align with the overall theme that U.S. government interest are more than a little deeply involved in the domestic surveillance system known as Twitter specifically, and big social media in general.

In the latest datapoint assembly, a solid dive by MintPressNews into the number of former FBI officials working at Twitter, shows just how enmeshed the federal police are with the social media platform. The scale is really quite remarkable. [SEE HERE]
Big picture – the number of FBI officials working for Twitter indicates some strong connective tissue behind both enterprises.
[MintPressNews] – […] The FBI is generally known as a domestic security and intelligence force. However, it has recently expanded its remit into cyberspace. “The FBI’s investigative authority is the broadest of all federal law enforcement agencies,” the “About” section of its website informs readers. “The FBI has divided its investigations into a number of programs, such as domestic and international terrorism, foreign counterintelligence [and] cyber crime,” it adds. (read more)
How would it damage the U.S. government if claims about the Chinese government having access to all user data on TikTok, are shown to be identical to the U.S. government having access to all user data on Twitter?
Let that question settle in for a few moments, because that is exactly what I have been alleging since, well, 2011, when the U.S. State Dept first collaborated with Twitter in a joint public-private partnership to use the platform as a communication tool exploiting the Arab Spring uprising in Egypt, Libya and beyond.

The issue of Jack’s Magic Coffee Shop is an issue of financial viability. The business model of Twitter just doesn’t exist as a free social media discussion platform while running the ultra-expensive data processing system needed for millions of simultaneous users. A global chat that requires exponential database responses as an outcome of simultaneous users is just ridiculously expensive. {Go Deep} However, if the computing system and massive database were being subsidized by the U.S. government, then the viability of the ‘free coffee‘ business model makes sense.
“Cloud computing is one of the core components of the strategy to help the IC discover, access and share critical information in an era of seemingly infinite data.” … “A test scenario described by GAO in its June 2013 bid protest opinion suggests the CIA sought to compare how the solutions presented by IBM and Amazon Web Services (AWS) could crunch massive data sets, commonly referred to as big data.” … “Solutions had to provide a “hosting environment for applications which process vast amounts of information in parallel on large clusters (thousands of nodes) of commodity hardware” using a platform called MapReduce. Through MapReduce, clusters were provisioned for computation and segmentation. Test runs assumed clusters were large enough to process 100 terabytes of raw input data. AWS’ solution received superior marks from CIA procurement officials”… (MORE)
The integration between Twitter and the United States Intelligence Community has been hiding in plain sight:
July 26, 2021, (Reuters) – A counterterrorism organization formed by some of the biggest U.S. tech companies including Facebook (FB.O) and Microsoft (MSFT.O) is significantly expanding the types of extremist content shared between firms in a key database, aiming to crack down on material from white supremacists and far-right militias, the group told Reuters.
Until now, the Global Internet Forum to Counter Terrorism’s (GIFCT) database has focused on videos and images from terrorist groups on a United Nations list and so has largely consisted of content from Islamist extremist organizations such as Islamic State, al Qaeda and the Taliban.
Over the next few months, the group will add attacker manifestos – often shared by sympathizers after white supremacist violence – and other publications and links flagged by U.N. initiative Tech Against Terrorism. It will use lists from intelligence-sharing group Five Eyes, adding URLs and PDFs from more groups, including the Proud Boys, the Three Percenters and neo-Nazis.
The firms, which include Twitter (TWTR.N) and Alphabet Inc’s (GOOGL.O) YouTube, share “hashes,” unique numerical representations of original pieces of content that have been removed from their services. Other platforms use these to identify the same content on their own sites in order to review or remove it. (more)
A shared hashing protocol is a form of data system integration.
The databases of the identified social media platforms appear to be integrated with the U.S. intelligence system. This relationship makes the U.S government a stakeholder in the financial sustainability of the enterprise(s). Thus, a collaborative effort to subsidize the underlying data processing fits the mutual benefit scenario.