Posted originally on Oct 7, 2025 by Martin Armstrong |
Health care spending has been at the forefront of the Democrats’ tantrum that led to the government shutdown. Where else do they plan to send tax dollars? The continuing resolution to keep the government open for another six months has a few stipulations that should raise questions.
The Corporation for Public Broadcasting (CPB) is to receive nearly half a billion dollars. The initial budget proposal presented by the Democrats included over $1.1 BILLION in taxpayer aid to broadcasting platforms like PBS and NPR.
Congress is on a perpetual vacation funded by the people. The people are demanding that these public servants work, and the Democrats believe that they deserve a $157 million raise for underperforming. All members of Congress are to be appointed personal security and residential security system. They are also requesting $10 million in security to the state office. Yet, the average American is forced to live in or near crime-ridden cities that these people insist are safe. Crime is a byproduct of MAGA rage, apparently, and only the politicians deserve to feel safe in America.
Dead Congressmen deserve a death gratuity, since they’re working equally as hard as their living peers. The temporary resolution includes a $174,000 payout to the families of Raul Grijalva (AZ), Gerald Connolly (VA), and Sylvester Turner (TX).
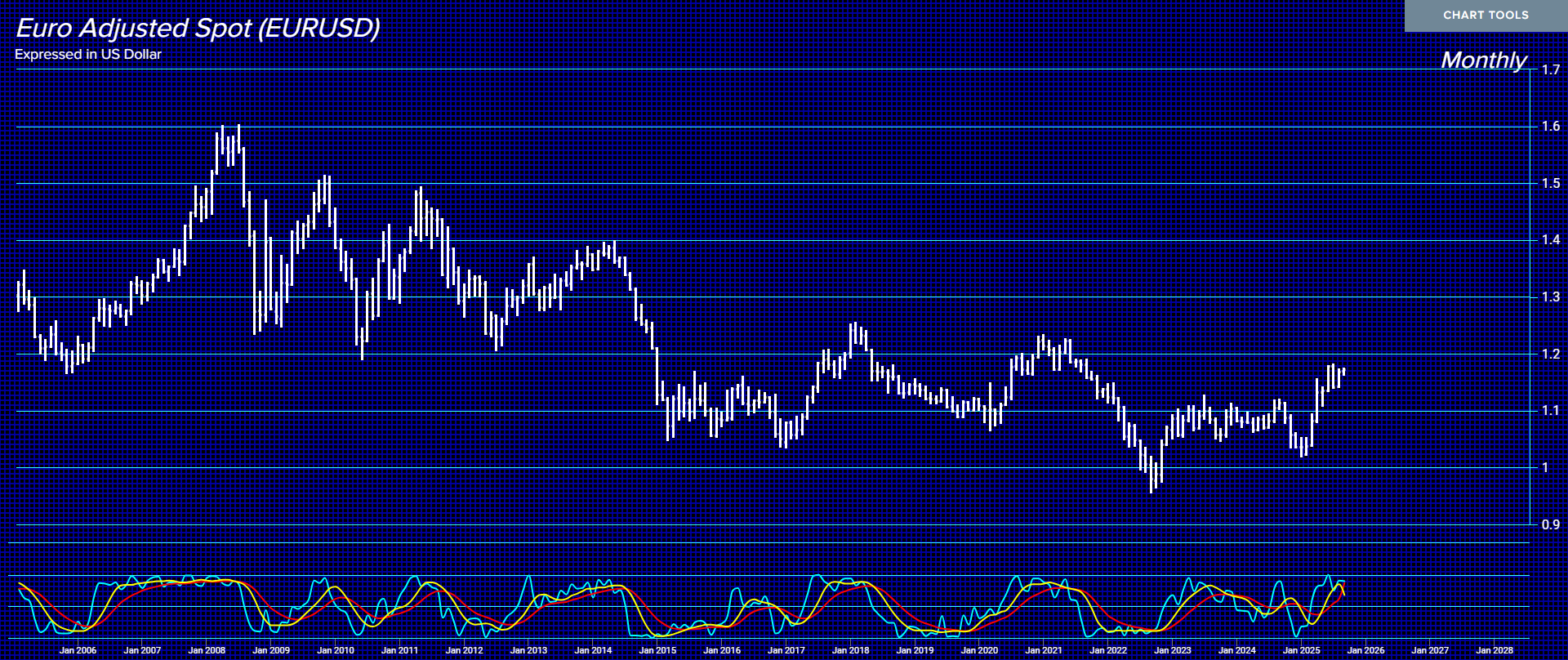
Here’s a kicker—the neocons are inserting their agenda within this bill and demanding that the US government allot $437 million to the European Bank of Reconstruction and Development. Countless aid has been sent to Ukraine, but the US government cannot operate unless we send another half-billion-dollar package.
Why should Americans be forced to spend on these extremely biased stipulations that do not benefit the people in any way?