Published originally on TrialSite News on April 20, 2022
Geert Vanden Bossche, DVM, PhD
General Manager at Voice for Science and Solidarity | The biggest challenge in vaccinology: Countering immune evasion

Table of content
- Key message
- Innate immunity: The child’s guardian angel
- There is no better example of how human immune intervention defies natural immunity than C-19 vaccination in children
- Children are particularly susceptible to immunological side-effects of the C-19 vaccines
- Vaccination of children in particular drives immune escape and dramatically diminishes the chance for generating herd immunity
- Omicron serves as an excellent live attenuated vaccine in healthy unvaccinated children. Vaccinating them with any of the current C-19 vaccines will only further increase instead of mitigating the selective immune pressure exerted by highly vaccinated populations and unquestionably take away the last glimmer of hope for generating herd immunity
- No single healthy child should be considered eligible for C-19 vaccination, neither from a public nor from an individual health viewpoint
- Summary and overall conclusion
Key message:
When a deep understanding of immunology, virology, vaccinology, evolutionary biology, and molecular biology is applied to analysis of whether children should receive current vaccines against COVID-19 (C-19), it is concluded that recommendation of such vaccination is scientifically unsound and that such vaccination is harmful to individual children, children as a group, and Humanity as a whole, for the following reasons:
- children have an abundant population of innate B cells that are capable of rapidly producing innate/ natural antibodies (Abs), mostly of IgM isotype, and that are highly adaptable to a broad and diversified spectrum of antigens or pathogenic agents. Innate Abs can facilitate cell-mediated killing of host cells infected with Coronaviruses (CoVs), including all SC-2 variants, independently of previous immune priming by antigen/pathogen encounters.
- innate immunity can be trained such as to acquire memory and, therefore, improve the host’s innate immune defense upon future exposure to more infectious variants that may emerge during an epidemic or pandemic.
- the C-19 vaccines undermine the innate immune system—by, for example, hindering binding of innate, low-affinity antibodies and by interfering with the normal training of a child’s innate immune system.
- By priming specific vaccine-induced immunity instead of exploiting the host’s pre-existing natural multi-specific immune defense, the C-19 vaccines prevent the development of optimal, sterilizing immunity in vaccinees.
- Whereas natural immunity (i.e., innate Ab-mediated killer cell immunity combined with neutralizing S(pike)-specific Abs acquired upon recovery from natural disease) contributes to generating herd immunity during a pandemic/ epidemic, neutralizing, S-specific vaccinal Abs do not. Since the vaccine prevents the development of optimal, sterilizing natural immunity, C-19 vaccines prevent the vaccinated child from contributing to building herd immunity during a SARS-CoV-2 (SC-2) pandemic.
- Since unvaccinated children’s immune systems contribute to the development of herd immunity against CoVs, they contribute a huge public health benefit. C-19 vaccination of children prevents this public health benefit.
- Priming the child’s immune system with C-19 vaccines is likely to further enhance immune escape and increase the infectiousness and virulence of future variants.
- Increasingly, it is unvaccinated children who will be best able to handle future infection by new SC-2 variants, compared to vaccinated children and vaccinated adults—because the unvaccinated have unhampered capacity to naturally activate innate Ab-mediated sterilizing immunity, whereas the vaccinated have compromised innate immunity and are prone to breakthrough infections (due to declining vaccinal Ab titers) and potentially predisposed to Ab-dependent enhancement of disease (due to suboptimal neutralizing capacity of vaccinal Abs).
- Compared to unvaccinated individuals, vaccinated individuals are more likely to become infected with SC-2 in case the virus becomes largely resistant to the potentially neutralizing vaccinal Abs—because, among other things, non-neutralizing vaccinal anti-S Abs actually facilitate entry of SC-2 into human epithelial cells of the upper respiratory tract.
- The vaccine’s interference with the function and training of a child’s innate immune system makes the vaccinated child more susceptible to not only C-19 disease, but also other viral (respiratory) diseases.
- In addition, the vaccines may provoke immune inflammatory and auto-reactive effects on individual vaccinees—causing vaccine-related side effects such as myocarditis, for example, and other potential autoimmune diseases.
- Bottom Line: There is compelling scientific evidence that the risks associated with C-19 vaccination far outweigh any benefits—at an individual level, at an evolutionary biology level, and at a herd immunity level.
Innate immunity: The child’s guardian angel
Innate immunity is a natural general protection that a person is born with. The innate immune system with which children are born is the reason that healthy children do not become severely ill with SC-2 infection. When they are exposed to the SC-2 virus, pre-existing immune effector cells of their innate immune system produce high concentrations of functional innate natural poly-specific antibodies (Abs) that are capable of recognizing all SC-2 variants and even all CoVs. These innate natural poly-specific antibodies are thought to recognize all SC-2 variants (and other CoVs) and are directed at true self-antigens (e.g., self-glycans) as well as self-mimicking antigen patterns on the virus. Self-mimicking glycan patterns are, for example, exposed on the surface of glycosylated enveloped viruses. Children who are born with rare genetic deficiencies of innate immune effector genes or whose innate immune defense is weakened due to underlying diseases may not benefit from a sufficiently strong protective immune response. However, these cases are the very rare exception and are not considered for the purpose of the following opinion piece.
There is also compelling evidence that innate immunity can be trained by epigenetic changes. The latter can change the immune response in such a way that innate immune cells respond more strongly towards a second exposure to the virus than to the initial exposure. Repeated challenges to SC-2 during the C-19 pandemic would already explain why ‘trained’ innate immune cells in older age groups (in contrast to naïve innate immune cells in children) may even lead to negative vaccine efficacy in these age groups (see attachment at the bottom; data Public Health Scotland and UK Health Security Agency; UKHSA).
The quality of one’s innate immune system is directly related to one’s overall health. If a person is healthy, has no underlying disease, has good nutrition, lives an active lifestyle, is in good physical and mental health, then that person will have good innate immunity.
There is a further layer of protection, if innate immunity is breached, and that is acquired (adaptive) immunity. In the case of an acute, self-limiting viral infection, if the innate immune system is able to reduce the bulk of the viral load but cannot eliminate all of the virus, such that some virus pushes through and causes disease – then nature has a backup, which is our acquired (adaptive) immune system. Acquired (adaptive) virus-specific Abs produced by immature B cells catch the particles of the virus that have breached our first line of innate immune defense and facilitate abrogation of infection by cytotoxic T cells, thereby enabling recovery from natural disease. Furthermore, the acquired (adaptive) immune system remembers this specific event and —by maturing virus-specific memory B cells (to produce neutralizing Abs of high affinity and specificity in the future) — is able to provide durable protection against future exposure to both the original virus and a broad spectrum of viral variants.
In the case of CoV, durable protection against infection is provided by both, the epigenetically trained poly-specific innate Abs and the S(pike)-specific Abs produced by adaptive immune system’s memory B cells. Since the innate immune response clears the bulk of viral load before the elicited S-specific Abs peak, the latter do not exert immune pressure on viral infectiousness. Based on all of the above, it follows that – even during a pandemic – natural immunity can trigger and sustain sterilizing immunity without driving immune escape. This already explains why a ‘natural’ pandemic of an acute, self-limiting viral infection will spontaneously generate herd immunity and, therefore, transition into an endemic phase. In contrast, neutralizing S-specific Abs induced by C-19 vaccines may not have sufficient neutralizing capacity to prevent infection when vaccination is performed during a pandemic. This inevitably leads to selective (i.e., S-directed) immune pressure on the circulating virus.
The innate immune system is equipped with extremely potent humoral and cellular effectors (i.e., innate Abs and natural killer cells, respectively) that are capable of preventing productive viral infection. Provided their presence in sufficiently high concentration and / or their training by previous exposure, innate Abs provide immediate, early and broad protection against several viral pathogens, including CoVs and Influenza viruses, making them a crucial non-redundant component of the humoral immune system.
Innate Abs are produced mainly, if not exclusively, by a subset of long-lived, self-replenishing B cells termed B-1 cells. It has been suggested that the unique developmental pattern of these B-1 cells, which rests on positive selection by self-antigens, ensures production of innate Abs expressing evolutionarily important specificities that are required for recognition of common pathogen-related rather than antigen-specific signals. Different repertoires of such antibody specificities collectively operate to maximize the flexibility of the host’s first line of immune defense in response to free-circulating self-antigens and different sets of invading pathogens that share similar self-like motifs. This already explains why innate Abs for SC-2 protect against all coronaviruses, including all their variants, but also influenza virus and most likely other glycosylated viruses causing acute disease (e.g., respiratory viruses such as influenza and respiratory syncytial virus). However, B-1 cells have evolved a unique response pattern that minimizes the risk of autoimmunity.
There is no better example of how human immune intervention defies natural immunity than C-19 vaccination in children
Children’s innate immune systems are, by their nature, robust and strong and that is why the vast majority of children who are exposed to SC-2 contract asymptomatic infection and the overwhelming majority of them are protected from severe C-19 disease, regardless of the characteristics of the SC-2 lineage they are exposed to. It is because of this innate immune system, that vaccination does not benefit children; in fact, vaccination may be detrimental in that acquired vaccine-induced Abs that are no longer capable of neutralizing highly infectious SC-2 variants may still bind to the virus and thereby outcompete naïve innate natural Abs of much lower affinity. In this way, adaptive vaccine-induced immunity, unfortunately, enables children to exert immune pressure on viral infectiousness (i.e., on S protein), especially when vaccinal Abs are naturally recalled over and over again due to the dominant circulation of more infectious viral variants. Furthermore, it cannot be ruled out that subneutralizing concentrations of vaccinal Abs complexed with SC-2 virions can cause 1st grade Ab-dependent enhancement of disease (ADED). 1st grade ADED may be due to predominant production of afucosylated Abs. It is not known whether synthesis of afucosylated Abs could be promoted as a result of suboptimal affinity of neutralizing anti-S Abs since afucosylated Abs are known to enhance the affinity of IgG for the IgG-Fc-receptor III family (FcγRIII), found on natural killer cells (and on subsets of other cells) in the immune system.
In the case of Omicron, preponderance of non-neutralizing over neutralizing Abs renders vaccinees more susceptible to infection as compared to non-vaccinated individuals. The more their vaccinal Abs are boosted (by additional booster shots or by the circulating virus), the more vaccinees will become susceptible to infection.
Vaccination interferes with development of herd immunity: Both naturally occurring Ab-mediated immune defenses (i.e., NK cell activation by innate Abs and cytotoxic T cell activation by acquired Abs) are capable of preventing or abrogating productive SC-2 infection and reducing transmission during a pandemic/ epidemic, thereby allowing the healthy & unvaccinated part of the population to contribute to herd immunity (naturally), which is in the public health benefit as the pandemic can only be terminated when herd immunity is achieved. This is in sharp contrast to the effect of vaccine-induced anti-S Abs, which exert selective immune pressure on viral infectiousness when present at high prevalence (mass vaccination!). In the case of Omicron, anti-S Abs are directed at both the receptor-binding domain and the N-terminal domain of the S protein (S-RBD and S-NTD, respectively); because these Abs are present at high prevalence (due to the high level of Omicron’s infectiousness in a highly vaccinated population), these Abs will exert additional immune pressure on viral infectiousness (as anti-S-RBD [Omicron] Abs also target the broadly neutralizing antigenic site within the RBD) as well as on viral virulence (as exposure to Omicron results in boosting of Abs directed against the conserved enhancing antigenic site comprised within NTD).
Because of the important contribution of the innate immune effector cells to protecting children from productive viral infection and hence, from disease, SC-2 is an infection in children in the same way that influenza is an infection in children but neither is a childhood disease. Children certainly catch SC-2 but due to their innate immunity the infection is mostly asymptomatic or only causing mild illness. It is not abnormal nor unusual for children to be ill or to have a day or two being unwell. Cases of severe disease in children are rare and almost no cases of death have been reported in the 1-19 age cohort. For the period 1 February 2021 to 31 December 2021, the number of deaths in England and Wales where C-19 was the only cause mentioned on the death certificate there were two males (< 1y; 15-19 y) and one female (10-14 years) according to Office for National Statistics. These findings are confirmed by the vaccine surveillance report published by UKHSA in March 2022 (see attachment). Of course, children with underlying diseases or older individuals with a weakened innate immune system may contract more severe symptoms and require hospitalization. Likewise, dominant circulation of highly infectious variants may lead to more frequent productive infection and more pronounced disease symptoms in children, as further explained below. It would be wrong, though, to conclude that this can be solved by a mass vaccination program as there can be no doubt that the fulminant expansion in prevalence of such highly infectious variants (e.g., Omicron) directly resulted from the mass vaccination program and that the continuation of this program is only going to further increase selective immune pressure and, therefore, further promote the expansion of even more infectious variants. It is important to note that in the case of Omicron, lack of neutralizing capacity exhibited by vaccine-induced Abs has now led to enhanced viral infectiousness in vaccinees, i.e., vaccinees are more susceptible to infection as compared to the non-vaccinated. This already explains why vaccine effectiveness has now dramatically declined, even in children (see also attachment at the bottom). When the virus breaks through the first line of children’s immune defense (i.e., the innate Ab-mediated immune defense), their immune system engages the next line of natural immune defense, i.e., cytotoxic T cells, the activation of which is likely triggered by the internalization into dendritic cells of virions that are complexed by S-specific Abs (IgMs) produced by immature B cells. In this way, the virus is eliminated in ways that do not generate selective immune pressure on viral infectiousness while enabling training of poly-specific Ab-producing innate immune effector cells. People who recover from C-19 disease (i.e., the overwhelming majority of children who contract symptomatic SC-2 infection) will ultimately develop full-fledged IgGs that rapidly neutralize the virus (including a broad spectrum of variants) upon re-exposure, whereas the trained innate immune system will take care of the remaining viral load by virtue of poly-specific innate Abs that have acquired a higher level of affinity for more infectious circulating variants.
The statements from governments and vaccination stakeholders that vaccination of children will provide them with improved protection from contracting severe disease defies nature and how our natural immune defense successfully deals with natural infection by enveloped glycosylated viruses known to predominantly cause acute self-limiting infection or disease. This includes training of innate Ab-secreting immune effector cells, which enables more effective recognition of SC-2 and all its variants and thereby improves protection against disease. Vaccine-induced protection, however, only protects against severe disease. In addition, this type of protection will likely be of short duration as it comes with substantial immune pressure on viral virulence.
Once Omicron will be replaced by a new family of variants that can overcome this immune pressure, the vaccines will no longer protect against severe disease. It is the polyreactive Abs in the innate immune system that protect healthy children and youngsters from (severe) disease. This mechanism of protection is fundamentally different from the one protecting vaccinated from severe disease. All non-live vaccines against acute infectious diseases are Ab-based. Ab-based viral vaccines protect against disease but never protect against severe disease only. Furthermore, viral vaccines that enhance the susceptibility of vaccinees to infection while protecting them from (severe) disease have not been described. It is, therefore, highly likely that the in vivo protection against severe disease – as claimed by the current C-19 vaccines – is not due to S-specific neutralizing Abs but to S-specific non-neutralizing Abs that are capable of both, enhancing viral infectiousness and hampering viral virulence. This particularly applies to infections caused by Omicron, which is known to be largely resistant to potentially neutralizing vaccinal Abs. When present in sufficient concentration, high affinity, S-specific Abs readily outcompete low affinity, multi-specific Abs for binding to the same antigen. Given the high viral infection rate and hence, great risk of re-exposure (and, therefore, natural boosting), it is reasonable to assume that many of those that are vaccinated experience long-lived functional suppression of their protective, polyreactive innate Abs and are thereby left to rely on vaccine-induced Abs immunity for protection against severe C-19 disease while becoming more susceptible to SC-2 infection and possibly also to infections caused by other glycosylated enveloped viruses that are normally recognized by the same innate Abs. This particularly applies to children as their innate immune effector cells are largely naïve for lack of immune training. In addition, as already mentioned above, protection against severe diseases is likely going to be short-lived due to the ongoing natural selection of new immune escape variants.
Children are particularly susceptible to immunological side-effects of the C-19 vaccines
Innate Abs bind with lower affinity to SC-2 than vaccinal Abs. Vaccinal Abs that fail to neutralize the virus but are still able to bind the virus may, therefore, diminish or even suppress binding of relevant (i.e., CoV-reactive) innate Abs to SC-2. As the vaccinal Abs are antigen-specific, they have a higher affinity for the virus and can outcompete polyreactive innate Abs, even if they do not neutralize it (like with Omicron, as discussed above). When vaccinal Abs are boosted, for example because of repeated exposure to ‘more infectious’ circulating variants, they can suppress innate self-protective Abs for a prolonged period of time. Prolonged suppression of relevant innate Abs by vaccinal Abs could lead to tolerance towards other respiratory viral pathogens and hence, cause enhanced susceptibility to other acute viral respiratory infections.
Innate self-protective Abs play an important role in discarding antigens derived from degraded or degenerated autologous host cells. Hence, prolonged suppression of relevant innate Abs by non-neutralizing vaccinal Abs may lead to lack of elimination of such altered self-antigens and, therefore, cause the host immune system to start attacking the body’s own cells / tissues. This implies that vaccination of children in the presence of variants that are largely resistant to neutralizing Abs could be at risk of causing autoimmune diseases.
It is not only the fact there is no beneficial effect to receive the vaccine and that a child may become more susceptible to other viral diseases or even autoimmune diseases but there is also a serious risk that certain vaccines, in particular genetic C-19 vaccines (e.g., mRNA vaccines), could already harm the child’s health shortly after their administration by causing immune-inflammatory side-effects (e.g., myocarditis). Side-effects that occur shortly after vaccine administration are of particular concern with genetic C-19 vaccines and merely add to the risks that should be taken into account in the risk/ benefit analysis of genetically based C-19 vaccines.
Highly infectious variants are likely to re-infect previously asymptomatically infected individuals shortly after their first exposure. Since previous asymptomatic infection raises short-lived concentrations of S-specific, non-neutralizing Abs, these individuals may become more susceptible to SC-2 infection. This particularly applies to young children as their innate Abs are largely naïve (i.e., produced by immature B cells) and can, therefore, readily be suppressed by S-specific Abs in young children. It is, therefore, not surprising that a pandemic of more infectious variants comes with an enhanced infection rate in young children. Because mass vaccination has resulted in the expansion in prevalence of more infectious variants, the above-mentioned observation is to be considered an (indirect) immunological side-effect of the mass vaccination program. Public Health authorities have argued that children are an important source of viral transmission. They don’t seem to understand that mass vaccination is the culprit of enhanced viral transmission, not the solution. Furthermore, it is currently unknown whether premature susceptibility to viral infections that innate Abs normally protect against could pose a new threat to the health and well-being of young children. It should, therefore, be investigated whether the enhanced incidence of hepatitis in young children (e.g., ages 2-5 years)., for example, could possibly result from such enhanced susceptibility. Data from UKHSA have shown, though, that children can rapidly mitigate their enhanced susceptibility to infection by virtue of training their innate immune system. This already explains why vaccine effectiveness has now become negative in these younger age groups as well (as already mentioned above). Previous asymptomatic/ mild infection does not prevent innate immune training as this type of infection does not prime the host immune system. This provides additional evidence that there is no health benefit in vaccinating young children.
As mRNA vaccines lead to uncontrolled in vivo synthesis of a protein (i.e., spike) that is decorated with self-glycans, vaccine-related immune inflammatory side-effects could occur many months after vaccination (expression of S protein has been reported to persist for up to several months) and may manifest in several different organs (expression of S protein has been demonstrated in several different organs). It cannot be ruled out that – in the presence of S-specific Abs – enhanced expression of S protein on the surface of transfected host tissue cells triggers fusion of those cells with healthy, non-transfected host cells and thereby leads to formation of syncytia and histopathological changes in general. Cell surface-expressed S protein has been shown to trigger trans fusion between infected and non-infected host tissue cells.
As soon as you start vaccinating with non-live vaccines, then acquired immunity is being engaged while natural, Ab-mediated immunity is bypassed. This is of course the intention of being vaccinated: so that a more specific antibody response can more effectively deal with the infection. However, if the virus a person has been vaccinated against significantly changes, then the specific adaptive Abs generated for that virus by the vaccine may no longer recognize it as well as before and it will fail to neutralize it. On the other hand, the broader innate immune response that may have been able to deal with the changed virus is crowded out by the adaptive vaccine-induced immune response, leaving one vulnerable to significant infection by viral variants or 1st ADED, the latter as a potential result of poor binding of neutralizing Abs to heterologous antigenic sites. From an immunological viewpoint, it is reasonable to assume that this is particularly relevant in individuals who are vaccinated shortly before their primary exposure to a viral variant (i.e., the S protein of which differs from the one provided by the vaccine) or whose innate immune effector cells are poorly trained, as is regularly the case in young children. But even if there is a reasonable fit between the circulating variant and the elicited S-specific Abs, basic virology teaches that – unless live attenuated vaccines are used – mass vaccination in the middle of a pandemic of a highly mutable virus such as SC-2, for example, is a recipe for immune escape and that viral variants that escape potentially neutralizing Abs will expand in prevalence in the population.
Vaccination of children in particular drives immune escape and dramatically diminishes the chance for generating herd immunity
When administered during a pandemic, C-19 vaccines cannot diminish viral transmission in the population, and can, therefore, not contribute to herd immunity. Young age groups have a particularly high capacity for contributing to herd immunity as they have strong functional innate Ab capacity and hence, a high potential for mediating broad Ab-mediated sterilizing immunity against CoV (presumably via non-selective innate IgM-mediated activation of NK cells and/ or activation of MHC-unrestricted cytotoxic CD8+ T cells mediated by broadly cross-reactive, acquired IgM). As vaccine-induced, S-specific neutralizing IgGs readily outcompete naïve innate Abs in young children, the selective immune pressure they place on viral infectiousness will only increase. As a result, ‘more infectious’ immune escape variants will enjoy a strong competitive advantage, which will accelerate their dominant propagation in the host population. By vaccinating children, their individual health is not only being potentially harmed but so is public health generally – compromising innate immunity of large parts of the population prevents herd immunity from being established and further enhances the adaptation of more infectious immune escape variants to the highly vaccinated population, thereby accelerating their dominance in the host population. Children’s healthy immune systems are the reservoirs to eliminate the virus and constitute an important source for generating herd immunity and diminishing the likelihood for more infectious variants to dominate.
Omicron serves as an excellent live attenuated vaccine in healthy unvaccinated children. Vaccinating them with any of the current C-19 vaccines will only further increase instead of mitigating the selective immune pressure exerted by highly vaccinated populations and unquestionably take away the last glimmer of hope for generating herd immunity
We can only get rid of the pandemic when we achieve herd immunity. Herd immunity is population immunity and by definition is only achieved when the viral transmission rate is low enough to ensure that the vulnerable people (i.e., those with a weak or immune suppressed health status) have a low probability of becoming infected. That is, the vulnerable are automatically protected by the herd immunity generated by the bulk of the population.
In my opinion, I consider that we had an opportunity to achieve herd immunity at the start of this pandemic which was interrupted by lock downs until mass vaccination started – these measures meant that the opportunity to achieve herd immunity in the early stages was lost. I consider that the opportunity to achieve herd immunity has now shrunk even further with the arrival of the Omicron variant because this variant has acquired a substantial level of resistance to the vaccinal Abs. As a result, non-neutralizing vaccinal Abs are now rendering the virus more infectious in vaccinees, which explains why the vast majority of the population is now more susceptible to infection. That is exactly the opposite of what mass vaccination was supposed to do. In the unvaccinated, however, Omicron is serving as a live attenuated vaccine in that it stimulates natural immunity in ways that do not discriminate between SC-2 variants and don’t exert immune pressure on viral infectiousness (i.e., via Ab-mediated abrogation of infection by polyreactive, MHC-unrestricted cytotoxic immune cells). This mechanism typically contributes to building herd immunity and termination of a pandemic of an acute, self-limiting viral disease. This means that only the unvaccinated part of the population is now contributing to herd immunity but, unfortunately, it also means that the latter is no longer within reach because large parts of the population have now become vaccinated.
Another benefit of live attenuated vaccines (i.e., Omicron in the unvaccinated) is that they are able to train innate immune effector cells, which therefore can even improve their recognition of the virus to ameliorate the protective effect of innate Abs. Immune effector cells that secrete innate Abs can be trained just like other innate immune effectors can be trained: by repeated exposure to what is called ‘pathogen-associated molecular patterns’. This is, in fact, nicely shown by the data published by the UK Health Security Agency, previously Public Health England and Public Health Scotland – where they have shown that basically with aging and also with more exposure to the pathogen, the number of cases in the unvaccinated people was dramatically reduced – even to an extent such that vaccine effectiveness has now become negative in the vast majority of age groups (see above).
No single healthy child should be considered eligible for C-19 vaccination, neither from a public nor from an individual health viewpoint
As vaccine-induced anti-S Abs cannot prevent productive viral infections in the host population, they cannot prevent natural selection of more infectious variants. Consequently, the induction of vaccinal Abs in large parts of the population promotes selective transmission of ‘more infectious’ variants and hence, prevents herd immunity from being established. The more people we vaccinate, the more and the faster the population will exert immune pressure on the life cycle of the virus. This is now at high risk of promoting the expansion of new variants that are not only more infectious but also much more virulent.
In contrast, naturally induced immunity sterilizes the virus in that it prevents or abrogates productive infection by circulating variants in ways that don’t provide more infectious variants with a competitive fitness advantage. Naturally induced immunity can, therefore, dramatically diminish viral transmission. This is, by the way, what explains the rapid/ steep decline in the infection, mortality and morbidity rate after a previous surge in cases during a natural pandemic. In the rather exceptional event that a non-vaccinated healthy child (i.e., without underlying diseases or immune deficiencies) would contract moderate disease, the child will not only recover from the disease but also develop acquired immunity, which is long-lived, directed against a diversified spectrum of SC-2 variants and will protect that child, even when the titers of acquired Abs are low (as this will enable trained innate Abs to come into the play). On the exceptional occasion that Omicron would break through the innate immune defense of a healthy child, or for that matter any unvaccinated healthy individual, to cause more serious disease, the patient can be successfully treated – that has always been acknowledged and can successfully be dealt with by early multidrug treatment. In this way, even patients who are at risk of developing serious disease can not only successfully recover but even contribute to herd immunity. The immune status of a person who recovered from C-19 is, therefore, very different from the one induced by a C-19 vaccine. Vaccinal anti-S Abs have a narrower spectrum and are, therefore, not only less protective towards infection by viral variants but also suspicious of causing ADED in case their binding to S on the circulating variant is too weak to neutralize the virus.
Omicron is now increasingly generating durable anti-infective immunity in the unvaccinated part of the population. However, given the infection-enhancing effect of non-neutralizing vaccinal Abs in vaccinees and their strong and frequent recall as a result of natural boosting (via Omicron!), herd immunity is no longer within reach in highly vaccinated populations. The more people we vaccinate, the more and the faster the population will exert immune pressure on the life cycle of the virus. This is now at high risk of promoting the expansion of new variants that are not only more infectious but also much more virulent. Along the same lines of reasoning, we should not vaccinate against the Omicron variant as mass vaccination against Omicron too will boost titers of non-neutralizing, i.e., infection-enhancing Abs and thereby inevitably further increase selective immune pressure on the virus and foster the propagation of far more dangerous variants that fully resist potentially neutralizing Abs. For this reason, it is vital that we leave healthy, unvaccinated people alone, that we leave healthy unvaccinated children alone, and that – instead – we diminish viral transmission by conducting large-scale antiviral chemoprophylaxis campaigns in highly vaccinated countries while protecting the vulnerable and enabling their access to early multidrug treatment.
Summary and overall conclusion
In summary, we can conclude as summarized below:
Because innate immune effector cells in young children are not trained to deal with highly infectious viruses, their innate Abs harbouring a repertoire of specificities targeted at enveloped glycosylated viruses can be readily outcompeted by high-affinity vaccinal Abs directed at S protein, even if these Abs do no longer neutralize the virus. Consequently, vaccination of children turns off their broadly poly-specific natural anti-viral immunity in exchange for S-specific vaccinal Abs that are becoming increasingly useless since their neutralizing capacity becomes more and more eroded because of enhanced escape of the mutated S protein on SC-2 from highly specific, potentially neutralizing Abs (a trend that has been clearly confirmed by molecular epidemiologists) while outcompeting protective innate Abs. Low vaccinal Ab titers are, therefore, at high risk of allowing for breakthrough infections in children who are exposed to viral variants.
In addition, vaccinal Abs with diminished neutralizing capacity towards SC-2 variants are likely to enhance the susceptibility of vaccinated children to 1st grade ADED and thereby making S-specific vaccinal Abs in vaccinees, and particularly in children, more dangerous.
Enhanced suppression of innate Abs by a sustained (pandemic!) high prevalence of elevated anti-S Abs in vaccinated children would also turn them into an excellent breeding ground for more infectious immune escape variants while likely rendering them more susceptible to other viral infections and auto-immune diseases.
On the basis of the above, there can be no doubt that the conclusion of the risk/ benefit analysis strongly and unambiguously argues against vaccinating children against SC-2 for the risk of administering C-19 vaccines to healthy children outweighs the benefit. Therefore, there is no benefit in synthetically protecting children with vaccines when their natural immunity produces a long-lasting immune response that is much safer and more efficient, both from an individual and public health viewpoint. Defying the child’s natural immune defense against SC-2, and several other acute self-limiting viral infections (e.g., Influenza), is an unforgivable sin!
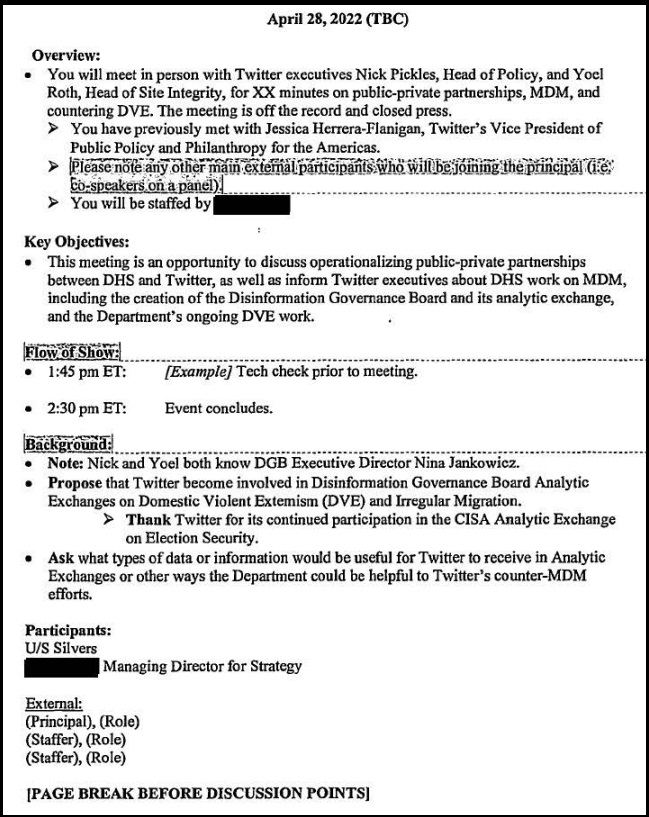
Attachment:
UK Health Security Agency
COVID-19 Vaccine Surveillance Report
Released March 31 2022
Data is March 1 – March 27
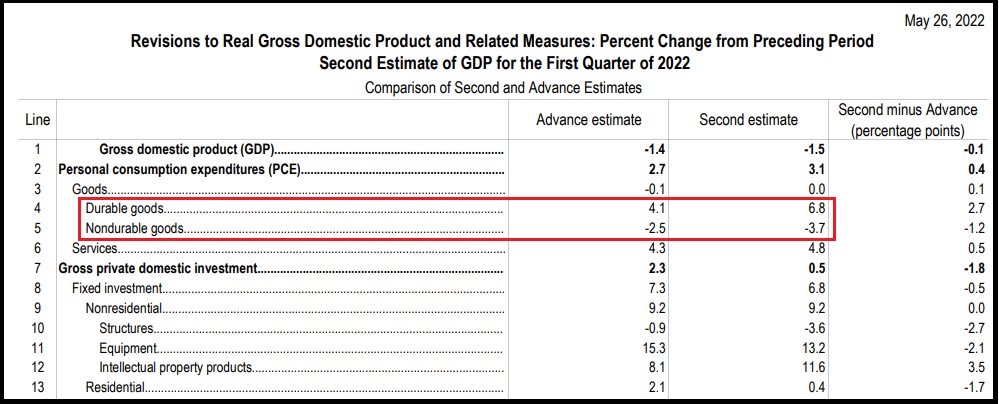
Summary of cases, hospitalizations and deaths:
One can view the back releases of this weekly report and see the trend toward diminished vaccine effectiveness emerge and grow steadily stronger since that time.
Cases
- For ages 18 and over, vaccination increased the rate of infection regardless of the number of doses, sometimes over 400%
- For ages under 18, 1 or 2 doses slightly increased the rate of infection
- For ages under 18, 3 or more doses (200,000 people out of over 64 million in the country) reduced rate of infection by only 30%
Hospitalizations
- For ages over 18, 3 or more doses decreased rate of hospitalizations by at most 40%, sometimes not at all
- For ages over 29, 1 or 2 doses increased rate of hospitalization for every age, sometimes by over 200%
Deaths
- For ages over 18, 3 or more doses decreased rate of death by at most 58%, but some age groups were as low as 16%
- For ages over 29, 1 or 2 doses increased rate of death for nearly every age group, often by over 200%
Overall, these data suggest that taking these vaccines greatly increases the spread of COVID.
That these vaccines give at most a mediocre reduction of negative outcomes, and only for a short time.
That these vaccines in every case cause a greater magnitude, long term, increase in negative outcome.
The data above are relate to COVID, not to any side-effects of the vaccines.
The LibreOffice spreadsheets are depicted below. They reflect the percent chance of case/hospitalization/death in (fully or partially) vaccinated vs unvaccinated.
March 2022 Chart of UK Case Rate % vs Unvaccinated by Doses (< 18 years):
The raw data can be found in the tables below.
Page 16 details the number of vaccinated individuals for each group with data covering the same dates:
80 and over Population: 2,725,031
3 Doses = 2,489,360
2 Doses = 2,566,995 – 2,489,360 = 77,635
1 Dose = 2,606,360 – 2,566,995 = 39,365
Unvaccinated = 2,725,031 – 2,606,360 = 118,671
70-79 Population: 4,979,828
3 Doses = 4,554,742
2 Doses = 4,705,335 – 4,554,742 = 150,593
1 Dose = 4,742,016 – 4,705,335 = 36,681
Unvaccinated = 4,979,828 – 4742016 = 237,812
60-69 Population: 6,420,555
3 Doses = 5,428,766
2 Doses = 5,818,926 – 5,428,766 = 390,160
1 Dose = 5,894,275 – 5,818,926 = 75,349
Unvaccinated = 6,420,555 – 5,894,275 = 526,280
50-59 Population: 8,374,446
3 Doses = 6,380,544
2 Doses = 7,251,305 – 6,380,544 = 870,761
1 Dose = 7,391,008 – 7,251,305 = 139,703
Unvaccinated = 8,374,446 – 7,391,008 = 983,438
40-49 Population: 8,228,211
3 Doses = 5,048,918
2 Doses = 6,395,752 – 5,048,918 = 1,346,834
1 Dose = 6,612,527 – 6,395,752 = 216,775
Unvaccinated = 8,228,211 – 6,612,527 = 1,615,684
30-39 Population: 9,478,334
3 Doses = 4,328,966
2 Doses = 6,405,034 – 4,328,966 = 2,076,068
1 Dose = 6,791,732 – 6,405,034 = 386,698
Unvaccinated = 9,478,334 – 6,791,732 
COVID-19ChildrenImmunologyVaccination
Comments (1)What do you think?
0/3000Publish
Apr. 21, 2022, 7:16 a.m.
Here’s a comment for you…There are unvaccinated adults among us who have not had one COVID-19 shot and are alive and well. Many of us over 60, even 70 years old are loving our natural immune systems’ gift to us and in gratitude have chosen to care for the immune system instead of provoking it artificially with synthetic mRNA. We are those childlike COVID warriors. Re: Quote “Omicron is serving as a live attenuated vaccine in that it stimulates natural immunity in ways that do not discriminate between SC-2 variants and don’t exert immune pressure on viral infectiousness (i.e., via Ab-mediated abrogation of infection by polyreactive, MHC-unrestricted cytotoxic immune cells). This mechanism typically contributes to building herd immunity and termination of a pandemic of an acute, self-limiting viral disease. This means that only the unvaccinated part of the population is now contributing to herd immunity…” LEAVE THE FOLLOWING OUT, THIS REST OF THE QUOTE – BECAUSE IT IS NOT UNIVERSALLY TRUE [“…but, unfortunately, it also means that the latter is no longer within reach because large parts of the population have now become vaccinated.”] and EMPHASIZE THIS QUOTE: “…leave healthy, unvaccinated people alone, that we leave healthy unvaccinated children alone, and that – instead – we diminish viral transmission by conducting large-scale antiviral chemoprophylaxis campaigns…”
Reply
Company
About UsTerms of ServicePrivacy PolicyContact Us
Publish on TrialSite
Writing Best PracticesWhy TrialSite?
TrialSiteNews
159 W Broadway, Suite 200
Salt Lake City, UT 84101