When previously questioned by Catherine Herridge about timing for declassification of documents President Trump noted “when they need them“. Within the response, who “they” were was never clarified; but the later directive to empower executive branch cabinet member AG Bill Barr provided a more clear reference.
In the legislative branch representatives Mark Meadows, Doug Collins and John Ratcliffe are the primary House members who were clearly helping to organize timing and distribution. Additionally, AG Barr has appointed a prosecutor in John H Durham to review the overall DOJ, FBI and intelligence community activity. Obviously Durham along with Inspector General Horowitz would benefit from declassification of documents in both of their reviews.

Earlier today John Ratcliffe outlined his view of U.S. Attorney John Durham as a benefactor of the declassification insofar as he would gain information for his review. Interestingly Ratcliffe noted Durham was essentially a ‘special counsel’ and could use access to documents as a tool toward a grand jury review [ergo DOJ declassification would be needed].
Along with noting the likelihood of Durham’s intent, Ratcliffe seemed to temper expectations of any upcoming publicly visible declassification.
The possibility of Durham exploiting/using documents declassified by his boss, AG Bill Barr, would suggest some of the material may not be made public; indeed that’s the inference from Ratcliffe earlier today as he outlined to Maria Bartiromo.
If accurate, it is worthwhile considering what *could be* publicly declassified by AG Barr, and yet not run afoul of any investigative value for Durham. Example: the declassification of the Rosenstein scope memos to Robert Mueller (no longer a reason to be hidden) would not seem to materially affect the investigative intents of Durham.
So considering investigative value, what documents could be purposefully made publicthat would not impede Durham?
Here’s the list of material possible for declassification. This was the original list as outlined in 2018:
- All versions of the Carter Page FISA applications (DOJ) (FBI) (ODNI).
- All of the Bruce Ohr 302’s filled out by the FBI. (FBI) (ODNI)
- All of Bruce Ohr’s emails (FBI) (DOJ) (CIA) (ODNI). All supportive documents and material provided by Bruce Ohr to the FBI. (FBI)
- All relevant documents pertaining to the supportive material within the FISA application. (FBI) (DOJ-NSD ) (DoS) (CIA) (DNI) (NSA) (ODNI);
- All intelligence documents that were presented to the Gang of Eight in 2016 that pertain to the FISA application used against U.S. person Carter Page; including all intelligence documents that may not have been presented to the FISA Court. (CIA) (FBI) (DOJ) (ODNI) (DoS) (NSA) Presumably this would include the recently revealed State Dept Kavalac email; and the FBI transcripts from wiretaps of George Papadopoulos (also listed in Carter Page FISA). [AKA ‘Bucket Five’]
- All unredacted text messages and email content between Lisa Page and Peter Strzok on all devices. (FBI) (DOJ) (DOJ-NSD) (ODNI)
- The originating CIA “EC” or two-page electronic communication from former CIA Director John Brennan to FBI Director James Comey that started Operation Crossfire Hurricane in July 2016. (CIA) (FBI) (ODNI)
Additionally, since the 2018 list was developed, more information has surfaced about underlying material. This added to the possibility of documents for declassification:
♦ President Trump can prove the July 31st, 2016, Crossfire Hurricane counterintelligence operation originated from a scheme within the intelligence apparatus by exposing the preceding CIA operation that created the originating “Electronic Communication” memo. Declassify that two-page “EC” document that Brennan gave to Comey. [The trail is found within the Weissmann report and the use of Alexander Downer – SEE HERE]
♦ Release and declassify all of the Comey memos that document the investigative steps taken by the FBI as an outcome of the operation coordinated by CIA Director John Brennan in early 2016. [The trail was memorialized by James Comey – SEE HERE]
♦ Reveal the November 2015 through April 2016 FISA-702 search query abuse by declassifying the April 2017 court opinion written by FISC Presiding Judge Rosemary Collyer. Show the FBI contractors behind the 85% fraudulent search queries. [Crowdstrike? Fusion-GPS? Nellie Ohr? Daniel Richman?] This was a weaponized surveillance and domestic political spying operation. [The trail was laid down in specific detail by Judge Collyer – SEE HERE]
♦ Subpoena former DOJ-NSD (National Security Division) head John Carlin, or haul him in front of a grand jury, and get his testimony about why he hid the abuse from the FISA court in October 2016; why the DOJ-NSD rushed the Carter Page application to beat NSA Director Admiral Mike Rogers to the FISA court; and why Carlin quit immediately thereafter.
♦ Prove the Carter Page FISA application (October 2016) was fraudulent and based on deceptions to the FISA Court. Declassify the entire document, and release the transcripts of those who signed the application(s); and/or depose those who have not yet testified. The creation of the Steele Dossier was the cover-up operation. [SEE HERE]
♦ Release all of the Lisa Page and Peter Strzok text messages without redactions. Let sunlight pour in on the actual conversation(s) that were taking place when Crossfire Hurricane (July ’16) and the FISA Application (Oct ’16) were taking place. The current redactions were made by the people who weaponized the intelligence system for political surveillance and spy operation. This is why Page and Strzok texts are redacted!
♦ Release all of Bruce Ohr 302’s, FBI notes from interviews and debriefing sessions, and other relevant documents associated with the interviews of Bruce Ohr and his internal communications. Including exculpatory evidence that Bruce Ohr may have shared with FBI Agent Joseph Pientka. [And get a deposition from this Pientka fella] Bruce Ohr is the courier, carrying information from those outside to those on the inside.
♦ Release the August 2nd, 2017, two-page scope memo provided by DAG Rod Rosenstein to special counsel Robert Mueller to advance the fraudulent Trump investigation, and initiate the more purposeful obstruction of justice investigation. Also Release the October 20th, 2017, second scope memo recently discovered. The Scope Memos are keys to unlocking the underlying spy/surveillance cover-up. [SEE HERE and SEE HERE]
It would appear the scope memos, Kavalec memo, original FISA application and transcript of Papadopoulos conversation with Halper etc. could be released without impeding a grand jury review (hinted by Ratcliffe today).
While CTH would argue that full public declassification of everything would be a better approach; thereby allowing Durham to use any/all evidence therein; I also accept that protecting the “FISA enabled” institutions is not considered in our preferred approach.
Protecting the *legal and national security value* of an appropriately applied “FISA process” seems to be key institutional objective for the principals (Barr, Coats, etc.). As such, there is an institutional tendency to defend process. It’s a tightrope.
If the Barr perspective includes the need to retain legitimate national security value within the processes previously abused, Barr may mitigate what is released. Again, a tight-rope where ‘We The People’ are expected to trust yet another official.
CTH accepts the possibility of honorable intent within Bill Barr, cautiously. The ‘trust’ bank account is overdrawn. Perhaps that’s why very cautious optimism, with frustratingly tempered short-term expectations, is the prudent analytical perspective.
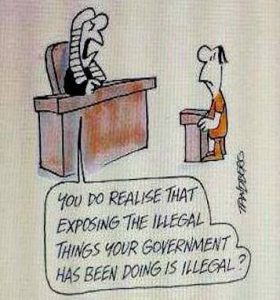
Then again, ‘We The People’ have no more tongue to bite…. A constitutional republic can only accept so much demonstrable corruption before all hell breaks loose.
I hope AG Barr understands this.

BARR: And look, I think if we — we are worried about foreign influence in the campaign? We should be because the heart of our system is the peaceful transfer of power through elections and what gives the government legitimacy is that process. And if foreign elements can come in and affect it, that’s bad for the republic. But by the same token, it’s just as, it’s just as dangerous to the continuation of self-government and our republican system, republic that we not allow government power, law enforcement or intelligence power, to play a role in politics, to intrude into politics, and affect elections.
JAN CRAWFORD: So it’s just as dangerous- So when we talk about foreign interference versus say a government abuse of power, which is more troubling?
WILLIAM BARR: Well they’re both, they’re both troubling.
JAN CRAWFORD: Equally?
WILLIAM BARR: In my mind, they are, sure. I mean, republics have fallen because of Praetorian Guard mentality where government officials get very arrogant, they identify the national interest with their own political preferences and they feel that anyone who has a different opinion, you know, is somehow an enemy of the state. And you know, there is that tendency that they know better and that, you know, they’re there to protect as guardians of the people. That can easily translate into essentially supervening the will of the majority and getting your own way as a government official.
JAN CRAWFORD: And you are concerned that that may have happened in 2016?
WILLIAM BARR: Well, I just think it has to be carefully look atbecause the use of foreign intelligence capabilities and counterintelligence capabilities against an American political campaign to me is unprecedented and it’s a serious red line that’s been crossed.
JAN CRAWFORD: Did that happen?
WILLIAM BARR: There were counterintelligence activities undertaken against the Trump Campaign. And I’m not saying there was not a basis for it, that it was legitimate, but I want to see what that basis was and make sure it was legitimate.
JAN CRAWFORD: So–
WILLIAM BARR: That’s one of the, you know, one of the key responsibilities of the Attorney General, core responsibilities of the Attorney General is to make sure that government power is not abused and that the right of Americans are not transgressed by abusive government power. That’s the responsibility of the Attorney General. (Transcript source)