May 27, 2019
Former U.S. Attorney to the District of Columbia, Joe diGenova, discusses the declassification of intelligence documents relating to political surveillance; and the origin of the database abuses outlined by FISC Presiding Judge Rosemary Collyer…
.
With President Trump returning from Japan tomorrow (5/28); and with the upcoming state visit to the U.K. coming June 3rd; a declassification “window of opportunity” opens between this Wednesday 5/29 and Saturday 6/2.
Given last weeks visit to Main Justice by congressman Mark Meadows; and considering the visit was specifically to review unredacted Page-Strzok-McCabe messages; it could be surmised the first series of declassified documents might be those communiques. Additionally, John Solomon has stated “Bucket Five” is likely the first release prior to the IG report:
Bucket Five – Intelligence documents that were presented to the Gang of Eight in 2016 that pertain to the FISA application used against U.S. person Carter Page; including all exculpatory intelligence documents that may not have been presented to the FISA Court. Presumably this would include the recently revealed State Dept Kavalac email; and the FBI transcripts from wiretaps of George Papadopoulos (also listed in Carter Page FISA).
Now that we have significant research files on the 2015 and 2016 political surveillance program; which includes the trail evident within the Weissmann/Mueller report; in combination with the Obama-era DOJ “secret research project” (their words, not mine); we are able to overlay the entire objective and gain a full understanding of how political surveillance was conducted over a period of approximately four to six years.
This is likely why there is institutional panic.
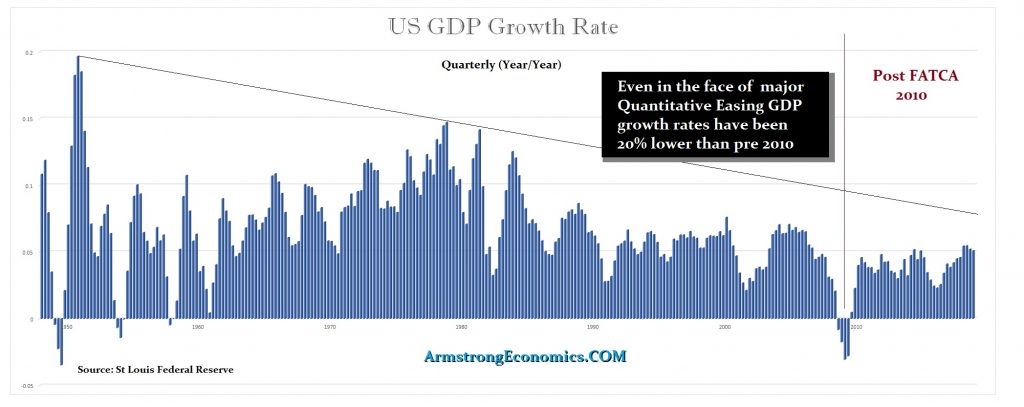
Working with a timeline, but also referencing origination material in 2015/2016 – CTH has tried to show how the program operated. The exploitation of government collected information explains an evolution from the IRS Files in 2010 to the FISA Files in 2016.
More importantly, research indicates the modern political exploitation of the NSA database, for weaponized intelligence surveillance of politicians, began mid 2012.
The FISA-702 database extraction process, and utilization of the protections within the smaller intelligence community, was the primary process. We start by reviewing the established record from the 99-page FISC opinion rendered by Presiding Judge Rosemary Collyer on April 26th, 2017; and explain the details within the FISC opinion.
I would strongly urge everyone to read the FISC report (full pdf below) because Judge Collyer outlines how the DOJ, which includes the FBI, had an “institutional lack of candor” in responses to the FISA court. In essence, the Obama administration was continually lying to the court about their activity, and the rate of fourth amendment violations for illegal searches and seizures of U.S. persons’ private information for multiple years.
Unfortunately, due to intelligence terminology Judge Collyer’s brief and ruling is not an easy read for anyone unfamiliar with the FISA processes outlined. The complexity also helps the media avoid discussing, and as a result most Americans have no idea the scale and scope of the issues. So we’ll try to break down the language.
.
For the sake of brevity and common understanding CTH will highlight the most pertinent segments showing just how systemic and troublesome the unlawful electronic surveillance was.
Early in 2016 NSA Director Admiral Mike Rogers was alerted to a significant uptick in FISA-702(17) “About” queries; these are searches using the FBI/NSA database that holds all metadata records on every form of electronic communication.
The NSA compliance officer alerted NSA Director Admiral Mike Rogers who then initiated a full compliance audit on/around March 9th, 2016, for the period of November 1st, 2015, through May 1st, 2016.
While the audit was ongoing, due to the severity of the results that were identified, Admiral Mike Rogers stopped anyone from using the 702(17) “about query” option, and went to the extraordinary step of blocking all FBI contractor access to the database on April 18, 2016(keep these dates in mind).
Here are some significant segments:
The key takeaway from these first paragraphs is how the search query results were exported from the NSA database to users who were not authorized to see the material. The FBI contractors were conducting searches and then removing, or ‘exporting’, the results. Later on, the FBI said all of the exported material was deleted.
Searching the highly classified NSA database is essentially a function of filling out search boxes to identify the user-initiated search parameter and get a return on the search result.
FISA-702(16) is a search of the system returning a U.S. person (“702”); and the “16” is a check box to initiate a search based on “To and From“. Example, if you put in a date and a phone number and check “16” as the search parameter the user will get the returns on everything “To and From” that identified phone number for the specific date. Calls, texts, contacts etc. Including results for the inbound and outbound contacts.
FISA-702(17) is a search of the system returning a U.S. person (702); and the “17” is a check box to initiate a search based on everything “About” the search qualifier. Example, if you put a date and a phone number and check “17” as the search parameter the user will get the returns of everything about that phone. Calls, texts, contacts, geolocation (or gps results), account information, user, service provider etc. As a result, 702(17) can actually be used to locate where the phone (and user) was located on a specific date or sequentially over a specific period of time which is simply a matter of changing the date parameters.
And that’s just from a phone number.
Search an ip address “about” and read all data into that server; put in an email address and gain everything about that account. Or use the electronic address of a GPS enabled vehicle (about) and you can withdraw more electronic data and monitor in real time. Search a credit card number and get everything about the account including what was purchased, where, when, etc. Search a bank account number, get everything about transactions and electronic records etc. Just about anything and everything can be electronically searched; everything has an electronic ‘identifier’.
The search parameter is only limited by the originating field filled out. Names, places, numbers, addresses, etc. By using the “About” parameter there may be thousands or millions of returns. Imagine if you put “@realdonaldtrump” into the search parameter? You could extract all following accounts who interacted on Twitter, or Facebook etc. You are only limited by your imagination and the scale of the electronic connectivity.
As you can see below, on March 9th, 2016, internal auditors noted the FBI was sharing “raw FISA information, including but not limited to Section 702-acquired information”.
In plain English the raw search returns were being shared with unknown entities without any attempt to “minimize” or redact the results. The person(s) attached to the results were named and obvious. There was no effort to hide their identity or protect their 4th amendment rights of privacy:
But what’s the scale here? This is where the story really lies.
Read this next excerpt carefully.
The operators were searching “U.S Persons”. The review of November 1, 2015, to May 1, 2016, showed “eighty-five percent of those queries” were unlawful or “non compliant”.
85% !! “representing [redacted number]”.
We can tell from the space of the redaction the number of searches were between 1,000 and 9,999 [five digits]. If we take the middle number of 5,000 – that means 4,250 unlawful searches out of 5,000.
The [five digit] amount (more than 1,000, less than 10,000), and 85% error rate, was captured in a six month period.
Also notice this very important quote: “many of these non-compliant queries involved the use of the same identifiers over different date ranges.” So they were searching the same phone number, email address, electronic “identifier”, or people, repeatedly over different dates. Specific people were being tracked/monitored.
Additionally, notice the last quote: “while the government reports it is unable to provide a reliable estimate of” these non lawful searches “since 2012, there is no apparent reason to believe the November 2015 [to] April 2016 coincided with an unusually high error rate”.
That means the 85% unlawful FISA-702(16)(17) database abuse has likely been happening since 2012. (Again, remember that date, 2012) Who was FBI Director? Who was his chief-of-staff? Who was CIA Director? ODNI? etc. Remember, the NSA is inside the Pentagon (Defense Dept) command structure. Who was Defense Secretary? And finally, who wrote and signed-off-on the January 2017 Intelligence Community Assessment?
Tens of thousands of searches over four years (since 2012), and 85% of them are illegal. The results were extracted for?…. (I believe this is all political opposition use; and I’ll explain why momentarily.)
OK, that’s the stunning scale; but who was involved?
Private contractors with access to “raw FISA information that went well beyond what was necessary to respond to FBI’s requests“:
 And as noted, the contractor access was finally halted on April 18th, 2016.
And as noted, the contractor access was finally halted on April 18th, 2016.
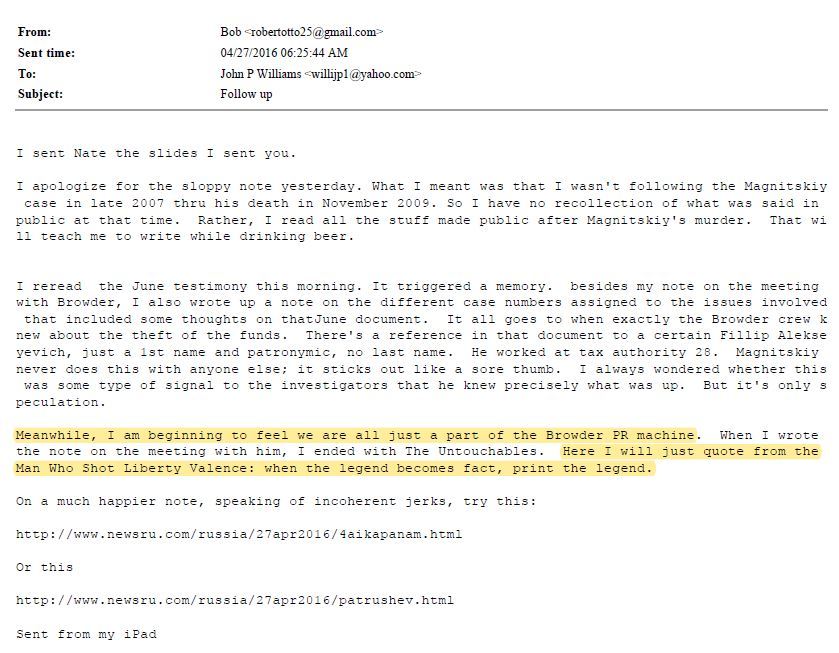
[Coincidentally (or not), the wife of Fusion-GPS founder Glenn Simpson, Mary Jacoby, goes to the White House the next day on April 19th, 2016.]
None of this is conspiracy theory.
All of this is laid out inside this 99-page opinion from FISC Presiding Judge Rosemary Collyer who also noted that none of this FISA abuse was accidental in a footnote on page 87: “deliberate decisionmaking“:
This specific footnote, if declassified, would be key. Note the phrase: “([redacted] access to FBI systems was the subject of an interagency memorandum of understanding entered into [redacted])”, this sentence has the potential to expose an internal decision; withheld from congress and the FISA court by the Obama administration; that outlines a process for access and distribution of surveillance data.
Note: “no notice of this practice was given to the FISC until 2016“, that is important.
Now, consider this footnote, and then reference THIS from 2012:
December 17, 2012
The Honorable Eric H. Holder, Jr.
Attorney General of the United States
United States Department of Justice
Washington, DC 20530
Dear General Holder:
Recently, the “Wall Street Journal” (WSJ) reported you granted the National Counterterrorism Center (NCTC) new powers to store dossiers on United States citizens, even if said citizens are not suspected of any criminal activity.
With these new powers, the NCTC would have the ability to copy entire government databases holding information on flight records, casino-employee lists, the names of Americans hosting foreign-exchange students, as well as other data.
The WSJ goes on to report the new rules allow the NCTC to keep data about innocent United States citizens for up to five years and to analyze it for suspicious patterns of behavior. Previously, both were prohibited.
If the WSJ report is accurate, these new powers represent a sweeping departure from past practices, which barred the NCTC from storing information about ordinary Americans unless a person was a terror suspect or the information sought was related to an investigation.
If the WSJ report is accurate, it raises numerous concerns and questions. As elected Representatives and members of the House Judiciary Committee, we are concerned such sweeping, fundamental changes would be made to existing policy without public input and Congressional approval. Changes, which fundamentally alter the relationship between the government and the governed, should only be made with input from the people by and through their elected Representatives. (more)
Summary of this aspect: The FISA court identified and quantified tens-of-thousands of search queries of the NSA/FBI database using the FISA-702(16)(17) system. The database was repeatedly used by persons with contractor access; who unlawfully searched and extracted the raw results without redacting the information; and shared it with an unknown number of entities.
The outlined process certainly points toward a political spying, surveillance, and file-building operation; and we are not the only one to think that’s what this system is being used for.
Back in 2017 when House Intelligence Committee Chairman Devin Nunes was working to reauthorize the FISA legislation, Nunes wrote a letter to ODNI Dan Coats about this specific issue:
SIDEBAR: To solve the issue, well, actually attempt to ensure it never happened again, NSA Director Admiral Mike Rogers eventually took away the “About” query option permanently in 2017. NSA Director Rogers said the abuse was so inherent there was no way to stop it except to remove the process completely. [SEE HERE] Additionally, the NSA database operates as a function of the Pentagon, so the Trump administration went one step further. On his last day as NSA Director Admiral Mike Rogers -together with ODNI Dan Coats- put U.S. cyber-command, the database steward, fully into the U.S. military as a full combatant command. [SEE HERE]
There is little doubt the FISA-702(16)(17) database system was used by Obama-era officials, from 2012 through April 2016, as a way to spy on their political opposition. Quite simply there is no other intellectually honest explanation for the scale and volume of database abuse that was taking place.
When we reconcile what was taking place and who was involved, then the actions of the exact same principle participants take on a jaw-dropping amount of clarity.
All of the action taken by CIA Director Brennan, FBI Director Comey, ODNI Clapper and Defense Secretary Ashton Carter make sense. Including their effort to get NSA Director Mike Rogers fired.
Everything after March 9th, 2016, was done to cover up the weaponization of the FISA database. [Explained Here] Spygate, Russia-Gate, the Steele Dossier, and even the 2017 Intelligence Community Assessment (drawn from the dossier and signed by the above) were needed to create a cover-story and protect themselves from discovery of this four year weaponization, political surveillance and unlawful spying. Even the appointment of Robert Mueller as special counsel makes sense; he was FBI Director when this began.
The beginning decision to use FISA(702) as a domestic surveillance and political spy mechanism appears to have started in/around 2012. Perhaps sometime shortly before the 2012 presidential election and before John Brennan left the White House and moved to CIA. However, there was an earlier version of data assembly that preceded this effort.
Political spying 1.0 was actually the weaponization of the IRS. This is where the term “Secret Research Project” originated as a description from the Obama team. It involved the U.S. Department of Justice under Eric Holder and the FBI under Robert Mueller. It never made sense why Eric Holder requested over 1 million tax records via CD ROM, until overlaying the timeline of the FISA abuse:
The IRS sent the FBI “21 disks constituting a 1.1 million page database of information from 501(c)(4) tax exempt organizations, to the Federal Bureau of Investigation.” The transaction occurred in October 2010 (link)
Why disks? Why send a stack of DISKS to the DOJ and FBI when there’s a pre-existing financial crimes unit within the IRS. All of the evidence within this sketchy operation came directly to the surface in early spring 2012.
The IRS scandal was never really about the IRS, it was always about the DOJ asking the IRS for the database of information. That is why it was transparently a conflict when the same DOJ was tasked with investigating the DOJ/IRS scandal. Additionally, Obama sent his chief-of-staff Jack Lew to become Treasury Secretary; effectively placing an ally to oversee/cover-up any issues. As Treasury Secretary Lew did just that.
Lesson Learned – It would appear the Obama administration learned a lesson from attempting to gather a large opposition research database operation inside a functioning organization large enough to have some good people that might blow the whistle.
The timeline reflects a few months after realizing the “Secret Research Project” was now worthless (June 2012), they focused more deliberately on a smaller network within the intelligence apparatus and began weaponizing the FBI/NSA database. If our hunch is correct, that is what will be visible in footnote #69:
 Additionally, Matt Gaetz appears to have seen “a memo held in the Congressional Sensitive Compartmented Information Facility (SCIF) that contained previously-undisclosed information involving the Federal Bureau of Intelligence (FBI) and Department of Justice (DOJ).” [LINK] Which sounds like the MOU in the footnote, and the memo that Trey Gowdy and Jason Chaffetz inquired about.
Additionally, Matt Gaetz appears to have seen “a memo held in the Congressional Sensitive Compartmented Information Facility (SCIF) that contained previously-undisclosed information involving the Federal Bureau of Intelligence (FBI) and Department of Justice (DOJ).” [LINK] Which sounds like the MOU in the footnote, and the memo that Trey Gowdy and Jason Chaffetz inquired about.
How this all comes together in 2019
Fusion GPS was not hired in April 2016 to research Donald Trump. As shown in the evidence provided by the FISC, the intelligence community was already doing surveillance and spy operations. The Obama administration already knew everything about the Trump campaign, and were monitoring everything by exploiting the FISA database.
However, after the NSA alerts in/around March 9th, 2016, and particularly after the April 18th shutdown of contractor access, the Obama intelligence community needed Fusion GPS to create a legal albeit ex post facto justification for the pre-existing surveillance and spy operations. Fusion GPS gave them that justification in the Steele Dossier.
That’s why the FBI small group, which later transitioned into the Mueller team, are so strongly committed to and defending the formation of the Steele Dossier and its dubious content. The Steele Dossier contains the cover-story and justification for the pre-existing surveillance operation.
During a rather innocuous podcast discussion panel April 12th, 2019, one of President Trump’s personal lawyers Jay Sekulow mentioned the FBI had three FISA applications denied by the FISA court in 2016. [Podcast Here – Note comment at 25:05] The denials were always suspected; however, until now no-one in/around the administration has ever confirmed.
If Sekulow is accurate, this adds additional context to the actions of the FBI in the aftermath of Admiral Mike Rogers and an increased urgency in gaining legal justification for surveillance and spy operation unlawfully taking place. A valid FISA warrant would help the FBI cover-up the surveillance. The likely targets were Manafort, Flynn and Papadopoulos…. but it appears the DOJ/FBI were rebuked.
These FISC denials would then initiate institutional panic dependent on the election outcome. An insurance policy would be needed. The Steele Dossier becomes the investigative virus the FBI wanted inside the system. To get the virus into official status, they used the FISA application as the delivery method and injected it into Carter Page. The FBI already knew Carter Page; essentially Carter Page was irrelevant, what they needed was the FISA warrant and the Dossier in the system {Go Deep}.
Fusion GPS was not hired to research Trump, the intelligence community was already doing surveillance and spy operations. The intelligence community needed Fusion GPS to give them a plausible justification for already existing surveillance and spy operations.
Fusion-GPS gave them the justification they needed for a FISA warrant with the Steele Dossier. Ultimately that’s why the Steele Dossier is so important; without it, the DOJ and FBI are naked with their FISA-702 abuse as outlined by John Ratcliffe.
No-one really knows the extent of the current documents and/or information that may be subject to the AG Bill Barr declassification. However, this is the original list as outlined in September 2018, and the agencies who would be involved in the declassification process:
- All versions of the Carter Page FISA applications (DOJ) (DoS) (FBI) (ODNI).
- All of the Bruce Ohr 302’s filled out by the FBI. (FBI) (ODNI)
- All of Bruce Ohr’s emails (FBI) (DOJ) (CIA) (ODNI), and supportive documents and material provided by Bruce Ohr to the FBI. (FBI)
- All relevant documents pertaining to the supportive material within the FISA application. (FBI) (DOJ-NSD ) (DoS) (CIA) (DNI) (NSA) (ODNI);
- All intelligence documents that were presented to the Gang of Eight in 2016 that pertain to the FISA application used against U.S. person Carter Page; including all exculpatory intelligence documents that may not have been presented to the FISA Court. (CIA) (FBI) (DOJ) (ODNI) (DoS) (NSA)
- All unredacted text messages and email content between Lisa Page and Peter Strzok on all devices. (FBI) (DOJ) (DOJ-NSD) (ODNI)
- The originating CIA “EC” or two-page electronic communication from former CIA Director John Brennan to FBI Director James Comey that started Operation Crossfire Hurricane in July 2016. (CIA) (FBI) (ODNI)
♦ President Trump can prove the July 31st, 2016, Crossfire Hurricane counterintelligence operation originated from a scheme within the intelligence apparatus by exposing the preceding CIA operation that created the originating “Electronic Communication” memo. Declassify that two-page “EC” document that Brennan gave to Comey. [The trail is found within the Weissmann report and the use of Alexander Downer – SEE HERE]
♦ Release and declassify all of the Comey memos that document the investigative steps taken by the FBI as an outcome of the operation coordinated by CIA Director John Brennan in early 2016. [The trail was memorialized by James Comey – SEE HERE]
♦ Reveal the November 2015 through April 2016 FISA-702 search query abuse by declassifying the April 2017 court opinion written by FISC Presiding Judge Rosemary Collyer. Show the FBI contractors behind the 85% fraudulent search queries. [Crowdstrike? Fusion-GPS? Nellie Ohr? Daniel Richman?] This was a weaponized surveillance and domestic political spying operation. [The trail was laid down in specific detail by Judge Collyer – SEE HERE]
♦ Subpoena former DOJ-NSD (National Security Division) head John Carlin, or haul him in front of a grand jury, and get his testimony about why he hid the abuse from the FISA court in October 2016; why the DOJ-NSD rushed the Carter Page application to beat NSA Director Admiral Mike Rogers to the FISA court; and why Carlin quit immediately thereafter.
♦ Prove the Carter Page FISA application (October 2016) was fraudulent and based on deceptions to the FISA Court. Declassify the entire document, and release the transcripts of those who signed the application(s); and/or depose those who have not yet testified. The creation of the Steele Dossier was the cover-up operation. [SEE HERE]
♦ Release all of the Lisa Page and Peter Strzok text messages without redactions. Let sunlight pour in on the actual conversation(s) that were taking place when Crossfire Hurricane (July ’16) and the FISA Application (Oct ’16) were taking place. The current redactions were made by the people who weaponized the intelligence system for political surveillance and spy operation. This is why Page and Strzok texts are redacted!
♦ Release all of Bruce Ohr 302’s, FBI notes from interviews and debriefing sessions, and other relevant documents associated with the interviews of Bruce Ohr and his internal communications. Including exculpatory evidence that Bruce Ohr may have shared with FBI Agent Joseph Pientka. [And get a deposition from this Pientka fella] Bruce Ohr is the courier, carrying information from those outside to those on the inside.
♦ Release the August 2nd, 2017, two-page scope memo provided by DAG Rod Rosenstein to special counsel Robert Mueller to advance the fraudulent Trump investigation, and initiate the more purposeful obstruction of justice investigation. Also Release the October 20th, 2017, second scope memo recently discovered. The Scope Memos are keys to unlocking the underlying spy/surveillance cover-up. [SEE HERE and SEE HERE]